Sending smartphone notifications from Ubiquiti EdgeRouter Lite
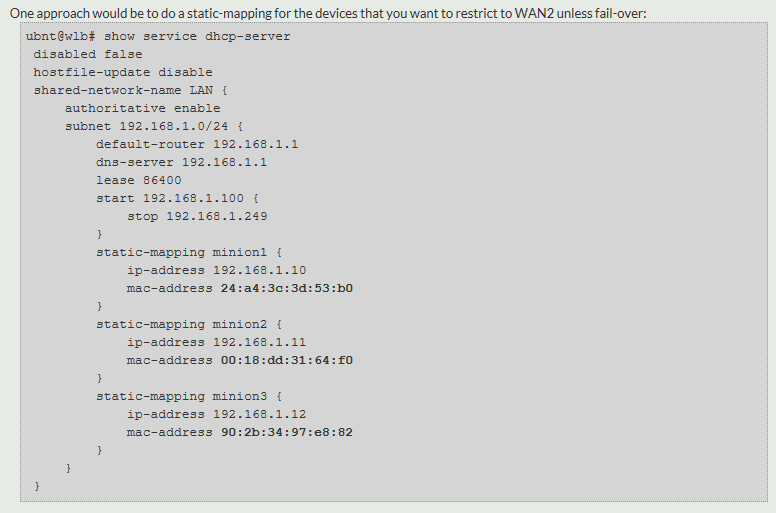
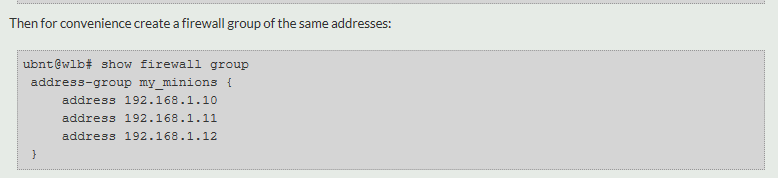
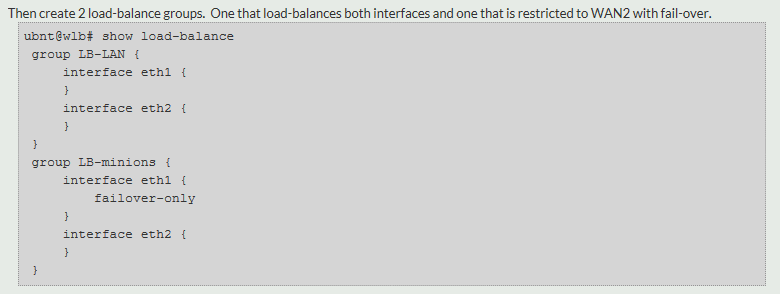
/Following on from my success of getting my Edge Router Lite to successfully run multiple load-balancing schemes for dual-WAN, and more importantly, assign different devices to different load balancing schemes, the next natural evolution was to send iPhone alerts when any of the links went down.
In principle it is quite easy, because the ERL already makes provision to run an arbitrary script when a link transitions (from active to inactive and vice versa). So, it's really just a question of having the right script.
If you Google, you'll find examples for sending email, but I wanted something more immediate (and less configuration effort - i.e. to not have to set up sendmail). Based on another example I considered using the pushover.net service, but wondered if I could use IFTTT to do the same, as I am already a user. (Saves me signing up to something new).
Turns out you can, by using their "webhooks" service; and turns out it's so simple, it's almost untrue.
IFTTT Webhooks allows you to generate simple triggers from a single web request
Step 1
First go to your IFTTT account and add the "webhooks" service. This will generate a unique key for you, which you need to make a note of. Annoyingly this is done in a font which does not distinguish between capital I and lowercase l, but you can regenerate the key, or paste into something where you can change the font.
Step 2
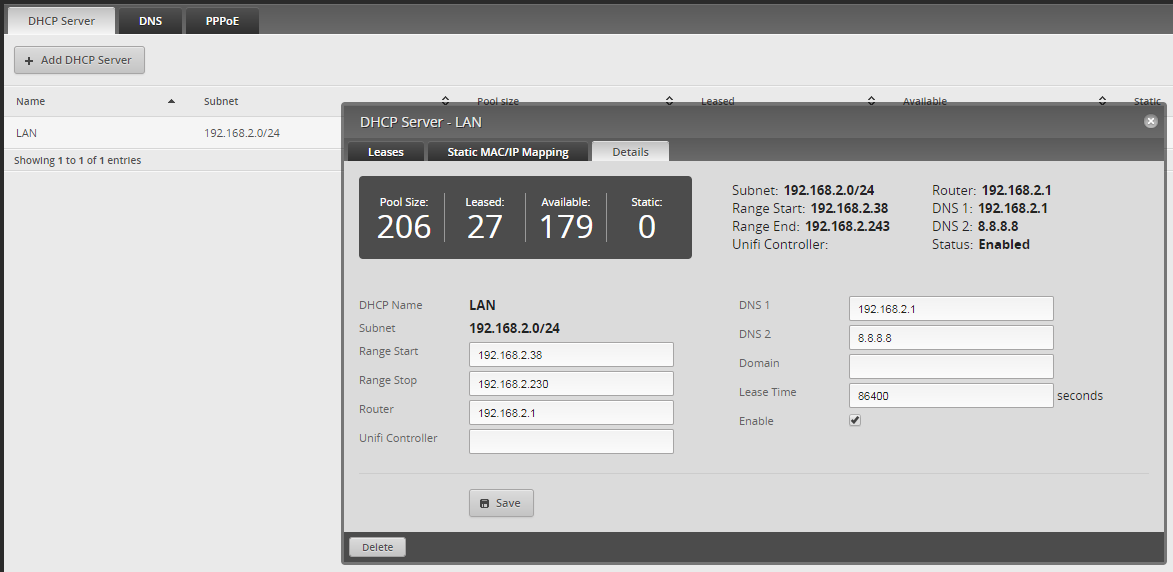
Next, log in to your Edge Router and navigate to /config/scripts and create the following script (I called mine failover-notify) :
A script to generate IFTTT phone notifications. Obviously use your own key.
Don't forget to make the script executable with the command chmod +x failover-notify
Step 3
Return to IFTTT and create an applet which uses the webhooks service as a trigger and the notifications service as the action:
Note how I have called the event "bb_failover". It is crucial this matches the name in your script (it comes in the URL after /trigger/ ). It is this name that allows you to configure many different triggers on IFTTT to do different things. Obviously you could use a different name, providing it matches in both places.
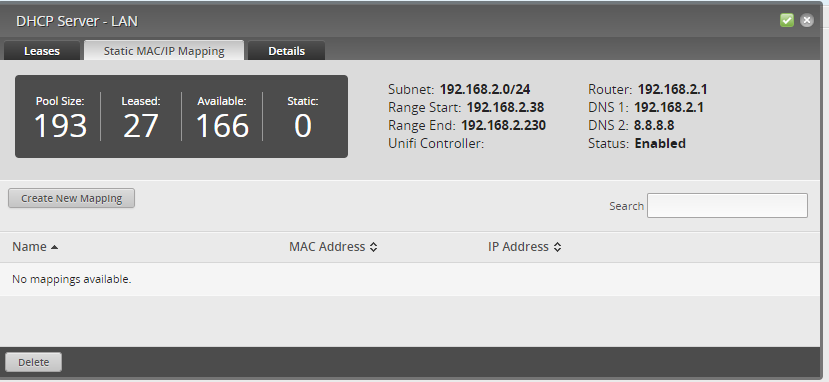
Value1 will be populated with the Load-Balance group name; Value2 will be the Port (eth0, eth1 etc.) and Value3 will be the status (either active or inactive).
Also, you will need the IFTTT app installed on your iPhone, to generate the notifications at the device end. (The app doesn't have to be running though).
Step 4
Return to the edge router for the final bit of configuration. You might want to test your script at this stage. If you type ./failover-notify A B C the script should run and give a success message, and shortly after you should get a notification on your phone. There's not much point proceeding until you can get this to work.
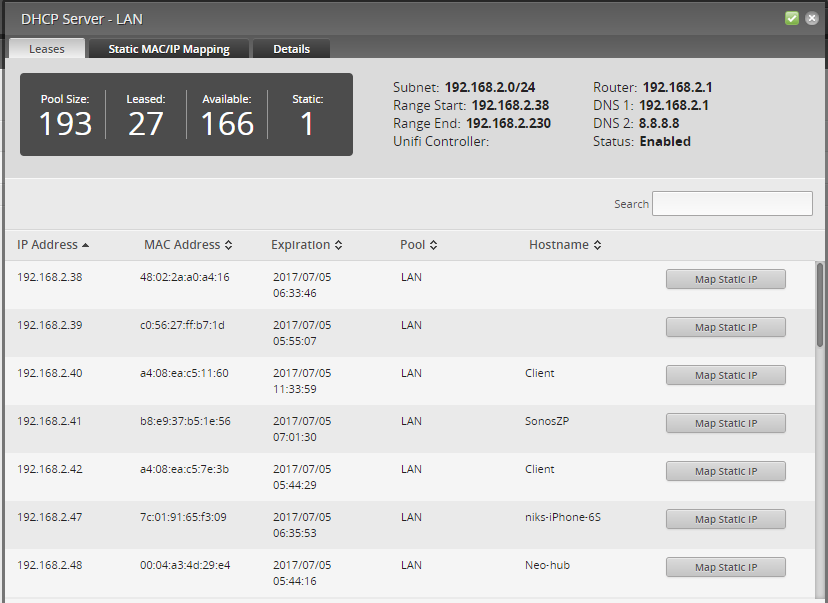
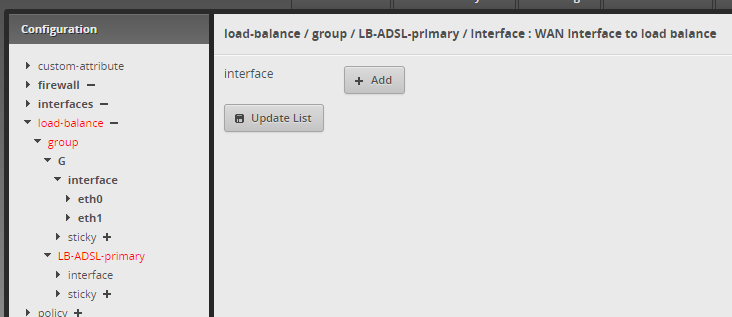
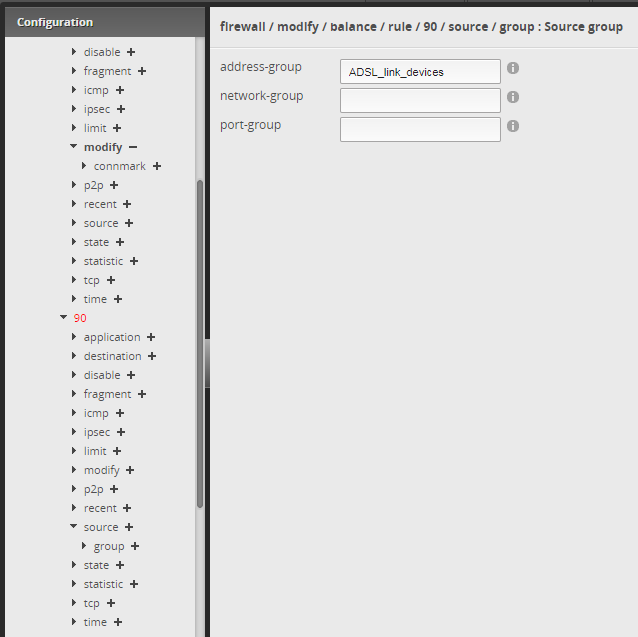
Once it does work, you can come out of the command line and go to the config tree. Here you choose the load-balance group you want the script to apply to.
Now, if you only have one group configured, you will apply it to that group. If, like me, you have more than one group, you might want to only apply it to one of the group to prevent duplicate alerts. This will depend on what your groups do and what alerts you want to get.
In my case, for example, both my load-balance group balance across both my only WAN links, so in fact I only need to apply it to one load-balance group, as both WAN links will be covered, and it doesn't matter which group I choose. I wouldn't apply it to both groups, as then I'd get double notifications - i.e. one from each.
Choose the Config-Tree tab and navigate to the load-balance group you want to monitor
After deciding which group(s) to receive notifications from, navigate to it, and put the full path to the script in the transition-script box, then click preview and save.
And that's it. Test it by disconnecting one of your WAN links, and see what happens!